1V1.LOL | Game Store

Select a product to continue
selected purchase
$ USD
FREE WITH OFFER
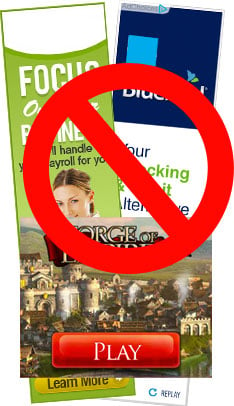
Please disable any pop-up blockers, ad blockers or firewalls. Also do not close the PayPal confirmation window. It must redirect back to our site to enable your purchase. If you have any issues please contact us.
Please disable any pop-up blockers, ad blockers or firewalls. Also do not close the PayPal confirmation window. It must redirect back to our site to enable your purchase. If you have any issues please contact us.